A lot of people assume that Tor is automatically secure, private and anonymous but it’s not really that simple. We all want to keep our online browsing anonymous in order to avoid unwanted monitoring. But it might take more work than you think.
So, is Tor anonymous? The truth is that there’s no simple answer to this question. As with anything, Tor comes with its own limitations and even a few risks. Read on to find out if Tor is anonymous and some important things you should know if you plan on using it.
Sniffed Exit Nodes

Before we answer the question is Tor anonymous, it’s important that you understand how it works. Basically, Tor re-routes your Internet traffic through its own internal network. This way your data must go through several layers of random relays before it actually exits the Tor networks. This is done to disguise where the traffic comes from so no-one can tell which computer sent the data.
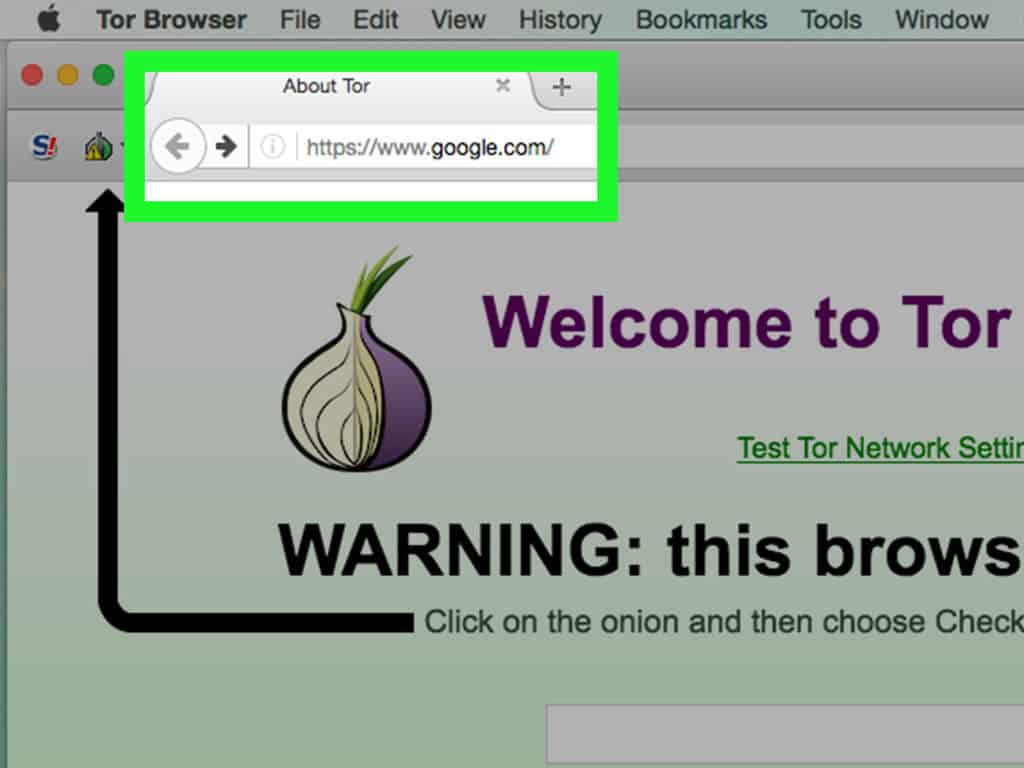
Nevertheless, Tor traffic is still going to come from the Tor network. For instance, if you do a Google search through Tor, your online traffic will go through layers and layers of Tor relays. But it will inevitably come out through the Tor network before it can connect to Google’s servers. Anyone with the right skills can monitor the final node from which your traffic comes out.
Note: Only visit encrypted websites (with HTTPS) when using Tor, especially if you plan to enter sensitive information and credentials. Anyone could be monitoring your private traffic data.
Attention: Read before you continue
Governments and ISPs across the world monitor their users online activities. If found streaming or browsing content on your Fire TV Stick, mobile or PC, you could get into serious trouble.
Currently, the following information is visible:
- Your IP:
- Your Country:
- Your City:
- Your ISP:
If this is your real information, you need to use a VPN to protect your identity.
We strongly recommend you to get a good VPN and hide your identity so that your online experience doesn’t take a bad turn.
We use IPVanish which is the fastest and most secure VPN in the industry. It is very easy to install on any device including Amazon Fire TV Stick. Also, it comes with a 30-day money-back guarantee. If you don’t like their service, you can always ask for a refund. IPVanish also runs a limited time offer where you can save 74% on your VPN and they allow you to use one account on unlimited devices.
This is a flash sale that can expire at any time!
IP Leaked by JavaScript and Plug-Ins
Is Tor safe when used in conjunction with Plugins and JavaScript? Well, it’s important to note that the Tor browser handle comes with pre-configured safety settings. This means you cannot use it to run plug-ins and Javascript will be completely disabled, while file downloads will typically show a warning.
Typically, Javascript is not a security risk but it can expose your IP address if you’re not careful. For instance, the JavaScript engine of your browser as well as plugins such as Adobe Flash can put you at risk of exposing your actual IP address to any website that wants to see it.
With the Tor browser bundle, you don’t have to worry about any of these problems because it comes with pre-configured settings. Of course, you could accidentally or intentionally use Tor browser plug-ins or JavaScript which effectively disables all of these protections.
Note: It’s very important that you leave the security settings provided by the Tor browser as they are and don’t try replacing Tor with any other browser. Rather stick with the provided settings and avoid any of the other applications that you see on the Tor network.
Why Exit Nodes Could Be Dangerous?
It’s quite tempting to want to run a Tor relay just to further protect your identity online. Basically, a Tor relay enables you to encrypt traffic within the Tor network.
With that said, running an exit relay might be risky because this is where Tor traffic leaves the safety of the anonymous network and goes into the Internet, which is like the Wild Wild West. For instance, there are many online criminals who use Tor for nefarious purposes and if their traffic happens to exit through your particular exit relay then it can be traced back to your IP address.
There was a case recently in Austria where a man was raided at his house and subsequently charged with child pornography charges because someone did the same thing with his Tor exit node. Therefore, it’s clear that operating a Tor exit node can significantly compromise your online safety. It’s like using a Wi-Fi network without protection from a VPN. For the most part, you may end up with a fine or a lawsuit for downloading or streaming copyrighted content. Basically, operating an exit node is very risky and it’s not recommended.
Note: The moral of the story here is to never run a Tor exit node.
Alternatively, you can run an exit node through a separate IP address through a Tor friendly ISP. This is a very tricky process and we don’t recommend it.
Why Use a VPN Service?
Is Tor anonymous? As you can see, there’s no clear-cut answer to this question. It all depends on how you use it, and there are definitely many measures you can take to secure your online connection. One such method is to use a VPN like IPVanish. We recommend IPVanish because it can completely hide your identity, private data, and location.
Did you find this article helpful? Let us know in the comments section below!

